What is Proper Awareness?
Published Date:
- March 6, 2026
An entire industry often offers customers products and services with little benefit. And they even buy into it!
Today in 2026, the cybersecurity awareness market will be worth around USD 6.7 billion [1]. Created just over 20 years ago, it is dominated by awareness or SAT providers, which I regard to be second generation. Companies such as Proofpoint, Terranova, Knowbe4, Sans, Sosafe, Hoxhunt, or whatever they are all called, secure the lion’s share of this market, which is expected to grow to just under USD 15 billion in 2031. In addition, there are hundreds of other players, such as CYBERDISE | Cybersecurity Awareness.
The striking thing about this offering, however, is that the products and services often do not aim to change behavior. Funny, standardized, and therefore useless phishing simulations are sold. Hours are wasted on boring information security training courses. Teachable moments are carried out and recorded in a playful manner, which may improve attitudes toward cyber risks, but not the effective behavior of individuals.
My conclusion after more than a decade of deep market knowledge: Much of what is offered in the field of cyber awareness is somehow reasonable, but – unfortunately – often with very limited impact.
But what really concerns me is that week after week I am confronted with CISOs and security engineers who want to change their existing cybersecurity awareness provider, but continue to demand the same approaches in terms of exercises or content, which in practice bring hardly any measurable security improvements!
They ask me for standard training courses, preferably a whole library full of them. Dynamic learning paths that lead to training modules or phishing exercises that are not – or hardly – personalized. Clearly, this is a dead end. And many don’t even realize it! Some don’t care, as long as they can tick a box somewhere. Gamification has also been a buzzword in recent years and is something I am asked repeatedly about. It’s true that playful and, at times, competition-based training courses are often perceived as less tedious. But their effective benefit is limited: gamification often changes knowledge – but not behavior under stress.
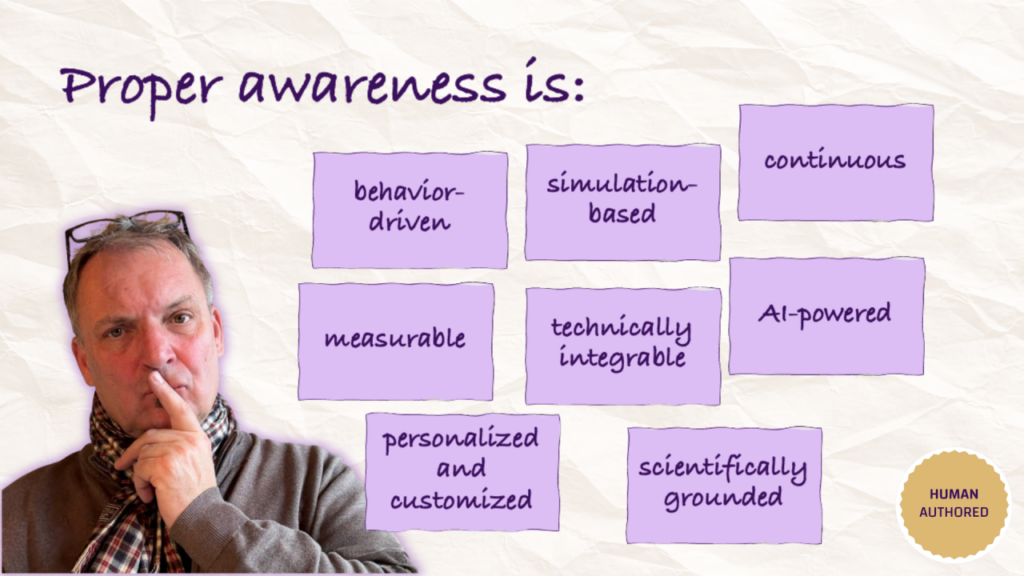
But what is proper awareness? Studies show that normative training improves attitudes, but only to a limited extent does it change actual behavior. Today, employees often know what would be right to do, but they act differently. Proper cybersecurity awareness therefore addresses:
- Achieving a healthy attitude toward risk
- An observable improvement in risk behavior
These are two different things and must be influenced specifically. A Lucerne University of Applied Sciences and Arts study from 2025 [2] shows that attack simulations are better than normative training. Personalized simulations, in turn work better than classic (standardized) phishing exercises, and AI/OSINT-supported spear phishing exposure improve risk behavior the most.
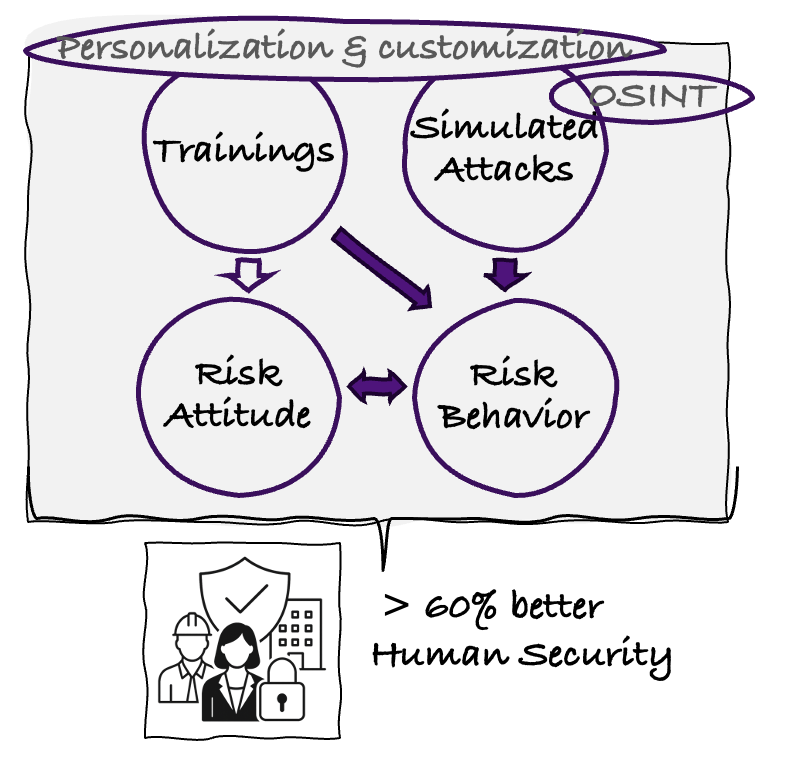
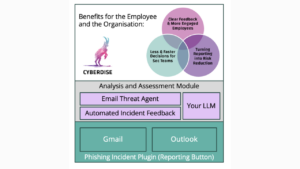
Furthermore, awareness must be continuous. Customers who do something twice a year would rather not bother and just save their money (I know, “if only the regulator weren’t there”). Misconduct should always be followed by an immediate learning impulse. Such events, like all other teachable moments – which should be kept short – must be embedded in a meaningful KPI structure. And then there’s repetition. Good awareness is repetitive. People only start to change when specialists like us are already sick and tired of the learning content! And then there’s AI: we now know that AI-generated spear phishing emails exceed the click rates of human experts[3]. If criminals are using AI, then we also need to train our employees with AI. The HSLU study also shows that the use of OSINT data in phishing exercises significantly increases awareness (Wow, how do they know such private things about me?).
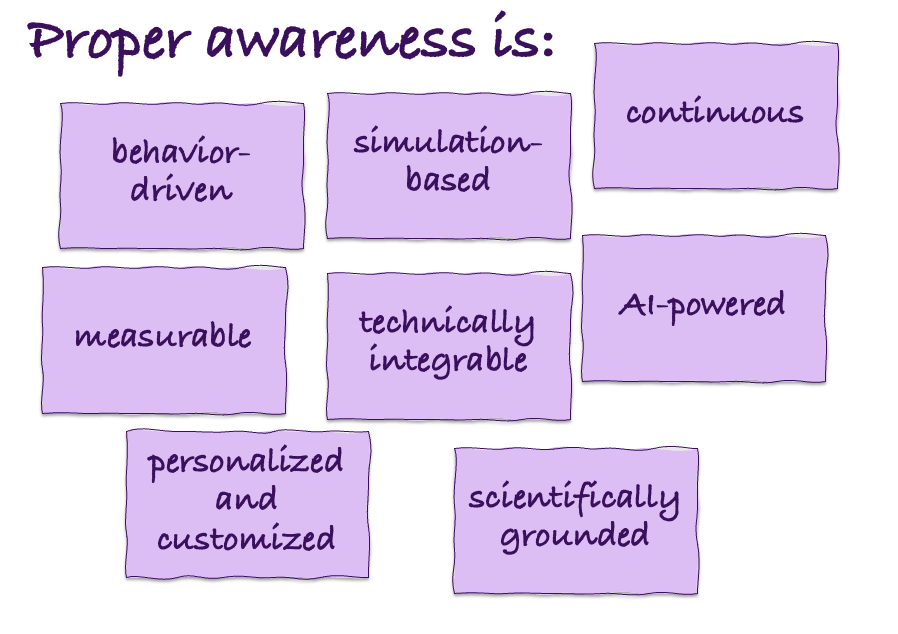
In summary, proper awareness is:
- Behavior-oriented
- Simulation-based
- Continuous
- Personalized and customized
- Measurable
- Technically integrable
- AI-supported, applying OSINT Data
- Scientifically sound
Everything else is just mandatory training!
Proper cybersecurity awareness means improving risk behavior, not just running training campaigns with nice courses or entertaining staff with phishing attempts that miles away from being realistic!
—
Am I alone in this assessment — or are others observing the same structural limitations in our industry?

We’re excited to share more cybersecurity insights, news, and updates with you in the upcoming editions of this newsletter. However, if you don’t find this helpful, we’re sorry to see you go. Please click the unsubscribe button below.